In the past year, ransomware has raked in millions for cybercriminals and their syndicates who both appear to have created the golden goose of malware.Sophos, with their blog post, has announced that WannaCry’s spiritual successor, SamSam ransomware has made $5.9 million in profit.
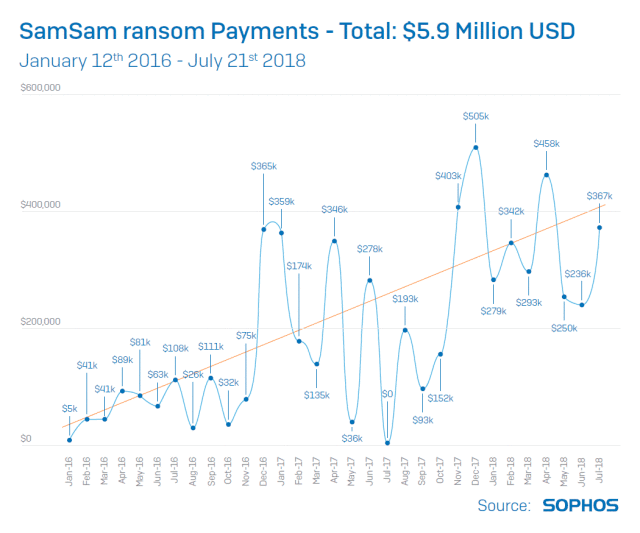
The line chart above supplied by Sophos details the profit episodes of SamSam since its inception. It is fairly noticeable the linear increase of ransom entering the coffers of SamSam’s virus authors, a very profitable trajectory since 2016.
The report emphasized: “SamSam is actually deployed to computers on the victim’s network in the same way, and with the same tools, as legitimate software applications. Based on the known victims, it’s been widely speculated until now that SamSam attacks are directed specifically at the healthcare, government and education sectors. Sophos can reveal that this is not the case. The money trail also revealed that SamSam has netted nearly $6 million in ransom payments – about six times more than the most recent best estimate.”
SamSam variants as time moves one gradually increase the asking price of the ransom to decrypt the user’s data. It used to be $9,600 ransom for 2016 ballooned to $40,000.
“If the SamSam attacker is on your network they will likely stay on it until they succeed unless they’re kicked off. Having gained access to a network, the SamSam operator uses a variety of tools to escalate their privileges to the level of Domain Admin. Then they scan the network for valuable targets and deploy and execute the malware as any self-respecting sysadmin might, using utilities such as PsExec or PaExec. Once it has been spread far and wide, the many copies of the ransomware are triggered centrally, starting within seconds of each other. On each infected machine, files are encrypted in a way that’s designed to cause the most damage in the shortest time,” the report further explained.
SamSam focuses on more damage against the victims, a more aggressive type of ransomware than the rest. “Most ransomware is spread in large, noisy and untargeted spam campaigns sent to thousands, or even hundreds of thousands, of people. They use simple techniques to infect victims and aim to raise money through large numbers of relatively small ransoms of perhaps a few hundred dollars each. SamSam is very different – it’s used in targeted attacks by a skilled team or individual who breaks into a victim’s network, surveils it and then runs the malware manually. The attacks are tailored to cause maximum damage and ransom demands are measured in the tens of thousands of dollars,” the report concluded.
The prevalence of Ransomware will not be forever, as cybercriminals have a new way to profit using the victim’s PC without actually harming the users. Such technique is replacing Ransomware as we speak, the so-called crytojacking malware. It is a revolutionary “product” for virus authors, as the new virus infects the machine to mine cryptocurrency using the resources of its victim PC. All mining is done in the background without the user realizing what is going on. We are in the age where Ransomware is still prevalent while crytojacking malware is still in its infancy. For a virus author, the future is very bright indeed.
